01. When performing a wireless integration, what must be configured for FortiNAC-F to provide the MAC address information of a connecting device?
a) MAC notification traps
b) Link traps
c) RADIUS
d) Syslog messaging
02. A user had full corporate network and internet access for most of the day but has now been isolated and is redirected to a quarantine/remediation webpage. What would cause this behavior?
a) The logged on user is not found in the active directory.
b) The host has been marked as failed for an admin scan.
c) The host has been administratively disabled.
d) The host was removed from the Registered Hosts group.
03. Two FortiNAC-F devices have been configured in a 1+1 active-passive HA configuration. Which condition would cause the primary FortiNAC-F to shut down the NAC process and change the management status to down?
a) The primary misses five heartbeats and fails to ping the gateway.
b) The secondary takes control of the primary.
c) An administrator changes the status of the secondary to Running – In Control.
d) The primary fails to poll the secondary while the gateway responds successfully.
04. How are logical networks assigned to endpoints?
a) Through device profiling rules
b) Through FortiGate IPv4 policies
c) Through model configuration settings
d) Through network access policies
05. An administrator wants to incorporate a third-party security device to generate security events and alarms. The third-party device is configured to send syslog messages to FortiNAC-F.
Which two items must be completed?
(Choose two.)
a) A security incident rule
b) A compliance policy
c) A security event parser
d) A trap MIB file
06. During an initial installation, which configuration must be applied to allow for the modeling of infrastructure devices?
a) set allowaccess dns
b) set allowaccess snmp
c) set allowaccess radius-auth
d) set allowaccess dhcp
07. An administrator wants to use FortiNAC-F to collect an application inventory for hosts. Which two options would satisfy this requirement?
(Choose two.)
a) Agent technology
b) MDM integration
c) Device profiling rules
d) Portal page on-boarding options
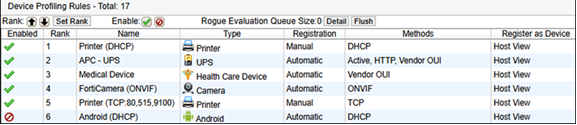
08. Refer to the exhibit.
If a device connects to the network for the first time, and FortiNAC-F does not receive a DHCP fingerprint, what would be the next step in the device profiling process?
a) The device would be modeled as a generic device.
b) After 5 minutes, the device would be evaluated against the next rule.
c) The FortiNAC-F would attempt to get a session fingerprint from a modeled firewall.
d) The device would be added to the database as a rogue.
09. A network administrator wants to use network access policies to define access for different types of hosts. Which group must be populated with all the possible points of connection?
a) Forced Registration
b) Role-Based access
c) Authorized access points
d) Forced Remediation
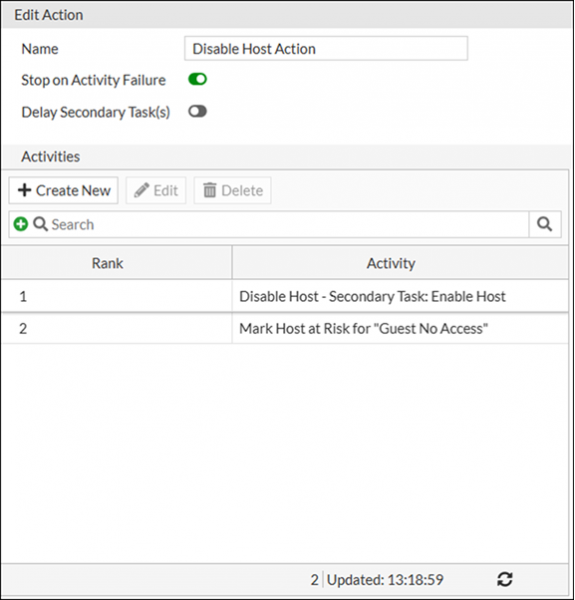
10. Refer to the exhibit.
An administrator adds an action to a security rule. What happens to the host that triggers the security rule?
a) The host is marked at risk.
b) The host is disabled but is not marked at risk until an administrator manually executes the secondary task.
c) The host is disabled, but no further action is taken.
d) The host is disabled and then marked at-risk.
 Before you write the Fortinet FortiNAC Administrator (NSE5_FNC_AD_7.6) certification exam, you may have certain doubts in your mind regarding the pattern of the test, the types of questions asked in it, the difficulty level of the questions and time required to complete the questions. These Fortinet Certified Professional - Secure Networking (FortiNAC Administrator) sample questions and demo exam help you in removing these doubts and prepare you to take the test.
Before you write the Fortinet FortiNAC Administrator (NSE5_FNC_AD_7.6) certification exam, you may have certain doubts in your mind regarding the pattern of the test, the types of questions asked in it, the difficulty level of the questions and time required to complete the questions. These Fortinet Certified Professional - Secure Networking (FortiNAC Administrator) sample questions and demo exam help you in removing these doubts and prepare you to take the test.